Office 365 Update Channels: Autopatch vs. Portal Management—Definitive Production Guide
You've deployed Microsoft 365 Apps via Intune, set the update channel in the configuration XML, and suddenly discover three different ways to manage updates: the XML generator at config.office.com, cloud update policies (servicing profiles) inside the same portal, and Microsoft Autopatch. Each promises to handle updates, but none clearly explain what happens when you switch channels—or whether it requires a reinstall.
This confusion costs enterprises weeks of testing and lost productivity during pilot programs. In this guide, drawn from hands‑on production deployments, we’ll map the complete update landscape, show you exactly which tool does what, and explain how channel switching actually works under the hood.
The Three Update Control Points—Architecture Overview
The Precedence Rule You Must Know
When a device checks for updates, the Office C2R engine reads policies in this exact order:
- Cloud servicing profile — If a profile (from config.office.com) targets this device/user, it wins. Checked first.
- Autopatch‑managed servicing profile — If the device is enrolled in Autopatch, Autopatch creates its own servicing profile. Only applies if no conflicting manual profile exists; conflict leads to unpredictable behaviour.
- Local XML configuration — The hardcoded channel in your Win32/ODT package. Used as ultimate fallback.
- Microsoft defaults — If all else is absent, device gets Current Channel (the most frequent update cadence).
Head-to-Head Comparison: When to Use Each
💻 Local XML (config.office.com)
Best for: Small, static environments where you deploy once and rarely change channels.
Pros:
- Free, no extra licensing
- Baked into the package; survives cloud sync failures
- Works offline after first install
Cons:
- To change channel, you must rebuild and redeploy the package
- No per-user granularity; entire device gets one channel
- Invisible in the servicing profile dashboard (no compliance reporting)
☁️ Cloud Servicing Profile (config.office.com)
Best for: Enterprise organizations that want cloud-managed, policy-driven control with audit trails.
Pros:
- Change channels instantly, no package rebuild
- Per-user, per-device targeting via Azure AD groups
- Built-in compliance reporting; shows what channel each device is on
- Included with Microsoft 365 Apps for enterprise (E3+)
Cons:
- Requires cloud connectivity; policy syncs every 24 hours
- Complex group targeting can conflict with Intune assignments
- Deferral days apply globally (hard to do rolling updates inside a single profile)
🚀 Microsoft Autopatch (Managed Updates)
Best for: Organizations that want Microsoft to schedule, test, and gate Office updates automatically.
Pros:
- Microsoft owns the testing and approval workflow
- Staged rollouts: ring 1 (early adopters) → ring 4 (broad population)
- Auto-delays updates if critical issues detected
- Works with Windows and other endpoints (not just Office)
Cons:
- Premium license required: Windows 10/11 Enterprise E3/E5 or Microsoft 365 E3/E5
- Less direct control; you accept Microsoft’s ring schedule
- If a manual servicing profile also targets the device, behaviour is undefined—pick one
- Adds another management plane if you try to mix Autopatch and manual profiles
🔀 Hybrid Approach (Recommended)
Best for: Large enterprises with mixed personas.
Pattern:
- Deploy with XML set to a safe default (e.g., Monthly Enterprise)
- Use servicing profiles to override specific groups (e.g., IT early‑adopter ring → Current Channel)
- Optionally enroll Autopatch for ring 1 only—remove any conflicting manual profiles for that ring
Benefit: Layers of control; fallback to XML if policy fails; cloud visibility via servicing profiles.
Channel Switching Without Reinstall—The Mechanism
This is the question that sparked the original Reddit post. The answer: yes, you can switch channels without reinstalling, but only if you follow the precedence rules correctly.
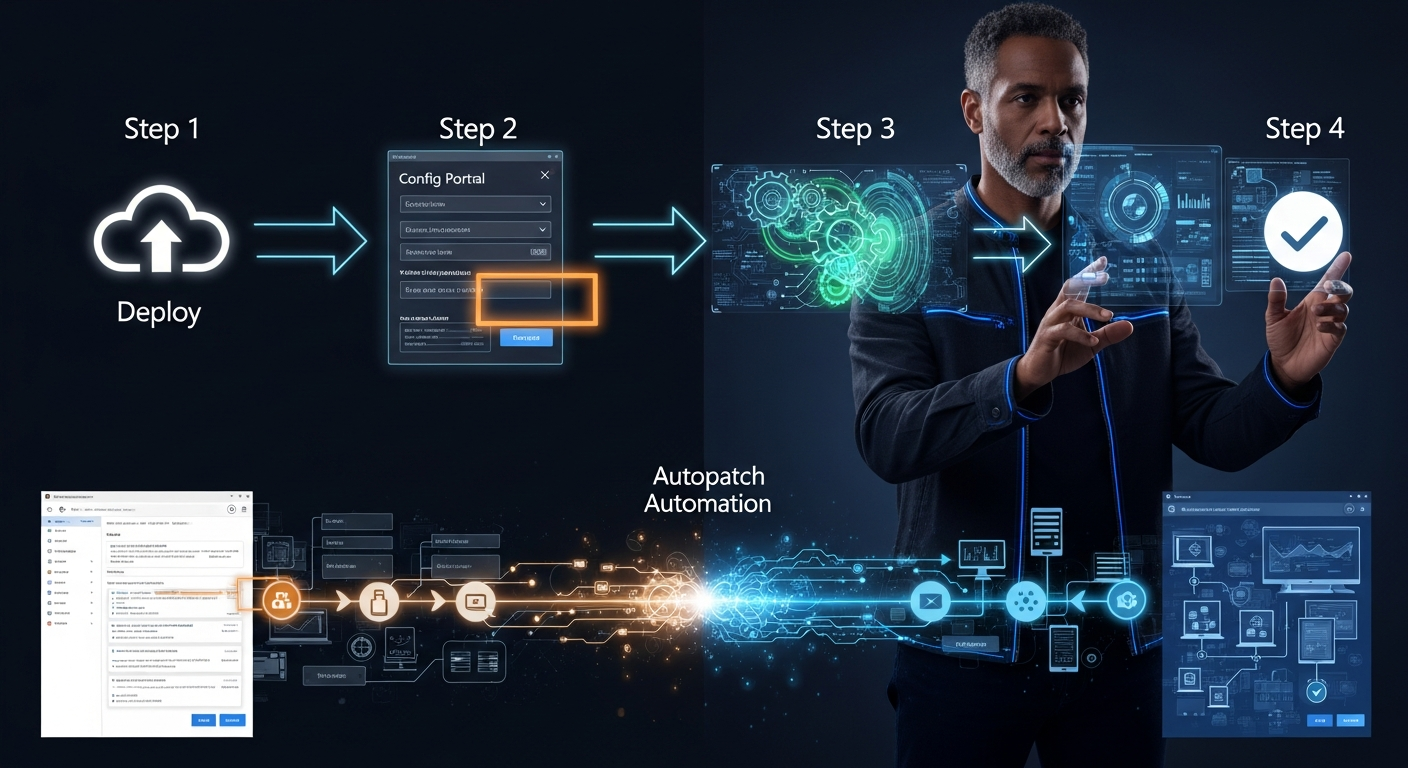
How to Switch Channels Using a Servicing Profile (Step-by-Step)
-
Navigate to the Microsoft 365 Apps admin center
Go to config.office.com → sign in with a Microsoft 365 admin account. (You need the Office Apps Admin or Global Admin role.)
-
Create or edit a servicing profile
Left sidebar → Servicing → Servicing profiles → Create profile (or select an existing one).
-
Set the update channel
Under Update channel, choose from:
- Current Channel — new features monthly
- Monthly Enterprise Channel — stable, updates 2nd Tuesday of month
- Semi-Annual Enterprise Channel — slow, updates in Jan & Jul only
-
Set deferral days (optional)
If you want a grace period before updates apply, set Defer updates by N days. Example: Current Channel + 7 days = users get new features 7 days after Microsoft releases them.
-
Assign the profile to device/user groups
Click Assignments → select Azure AD group(s). Policy applies to all devices in those groups within 24 hours.
Tip: Create an “Office Early Adopters” group for Current Channel and a broader group for Monthly Enterprise. This avoids surprises.
-
Verify and monitor
Return to Servicing profiles → click your profile → Device status tab shows which devices have applied the policy and what channel they’re on. Green checkmarks = compliant.
The Autopatch Wild Card
Microsoft Autopatch is fundamentally different from the other two. It doesn’t replace channels; it schedules updates within a channel—by automatically creating its own servicing profiles.
If you enroll Office in Autopatch:
- You still end up with a target channel (Current, Monthly Enterprise, etc.)—but it’s defined by the Autopatch‑managed profile, not by a manual one.
- Autopatch divides your org into four rings (test, staged, broad, finalize) and rolls out updates on Microsoft’s schedule, not yours.
- Updates only move between channels (e.g., Current → Monthly Enterprise) if you change the channel setting inside Autopatch.
- Autopatch is ideal if you want “zero‑touch” updates, but only if your org can accept Microsoft’s ring schedule.
Quick Reference: Which Control Method Wins?
| Scenario | Winner | Behavior |
|---|---|---|
| Servicing profile exists + Local XML present | Servicing profile | Cloud policy wins; XML ignored. Update via delta (no reinstall). |
| Autopatch enrolled + manual servicing profile active | ❌ Conflict | Unspecified by Microsoft. Avoid this configuration. |
| Only local XML, no servicing profile, Autopatch off | Local XML | Device uses the hardcoded channel. Changes require package rebuild. |
| Autopatch only (no manual profile) | Autopatch profile | Autopatch’s servicing profile governs channel and rollout cadence. |
| Device offline > 30 days, cloud policy unsynced | Local XML | Falls back to XML; no network = no cloud policy applied. |
Real-World Recommendation: Hybrid Three-Layer Approach
After dozens of deployments, this is the pattern that minimizes risk and maximizes control:
Practical Checklist: Before You Deploy
- ☑ Decide on your core channel (Monthly Enterprise recommended for most orgs)
- ☑ Use config.office.com Customization tool to generate XML with this core channel
- ☑ Package into a Win32 app via Intune (or use the built‑in Microsoft 365 Apps deployment)
- ☑ Define your ring strategy: IT test → Corporate standard → Sensitive/specialized
- ☑ Create Azure AD groups for each ring (e.g., “Office_Ring1_EarlyAdopters”)
- ☑ Create servicing profiles (one per ring) with appropriate channels and deferrals
- ☑ In each profile, assign the corresponding Azure AD group
- ☑ If premium licensed: consider Autopatch only for Ring 1; remove any manual profile for that ring
- ☑ Run pilot: deploy to Ring 1, watch for 2 weeks. Monitor servicing profile status for compliance
- ☑ If pilot succeeds: rollout to Ring 2, then Ring 3 (1–2 week intervals)
- ☑ Document your decision: which method you chose and why, for future admins
Troubleshooting: Device Not Updating to New Channel
You assigned a servicing profile, waited 24 hours, and the device is still on the old channel. Here’s the diagnostic workflow:
-
Check if the profile was assigned to the device
In config.office.com, click your servicing profile → Device status tab. Does the device appear in the list? If not, verify Azure AD group membership.
-
Force an immediate policy sync
On the device, open Command Prompt (as admin) and run:
// Force Office to check for cloud policies and updates "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeC2RClient.exe" /update user
This triggers a policy sync without restarting Office.
-
Check the active channel in registry
Run PowerShell:
Get-ItemProperty "HKLM:\SOFTWARE\Microsoft\Office\ClickToRun\Configuration" -Name "CDNBaseUrl"
The CDNBaseUrl value reveals the channel the device is actually using. Compare it with the expected channel URL from your servicing profile.
-
Look for conflicting policies
If you have both a servicing profile and local XML, and they conflict, the profile should win—but if the device can’t sync, XML is used. Check both.
-
Review Office C2R logs
On the device:
// C2R update logs C:\Users\[username]\AppData\Local\Microsoft\Office\16.0\OfficeClickToRunLogsLook for entries with “Channel” or “Update” to see what C2R attempted and why it might have failed (network timeout, no licence for Semi‑Annual, etc.).
Key Takeaways: The Decision Tree
Use local XML (config.office.com) if:
- You have < 500 users and rarely change update channels
- You want zero cloud dependencies; offline devices must still update
- You have no Microsoft 365 premium licensing for servicing profiles
Use cloud servicing profiles if:
- You need to change channels quickly for specific groups (no repackaging)
- You want compliance reporting (who’s on what channel)
- You use a ring strategy (early adopters, broad, conservative)
- This is the standard choice for most modern enterprises
Use Autopatch if:
- You have Windows 10/11 Enterprise E3/E5 or Microsoft 365 E3/E5 licensing
- You want Microsoft to own the testing + approval workflow
- Your org is OK with Microsoft’s ring schedule (you don’t define exact deployment dates)
- Use it instead of manual servicing profiles for the enrolled devices—not alongside
Use the Hybrid (Three-Layer) Approach for maximum resilience: XML fallback + servicing profile override + optional Autopatch gating for a dedicated ring (with no manual profile overlap).